Multifactor authentication (MFA) is considered a staple in the world of security. For many, the use of MFA may seem straightforward, but as with many things in life, complexities abound. In this article, we will discuss five current challenges associated with MFA and ways to mitigate those risks.
Before you go any further, visit this article over What is Multifactor Authentication? This article provides an overview of MFA, financial institution regulatory guidance sources, and tips for how to incorporate it into your information security program.
Challenge #1. Misapplication of MFA may negate your cyber insurance.
It is not a secret that cyber insurance companies are facing an uphill battle. Some sources state that in 2020, cyber insurers had a loss ratio of 500%, which means that for every $1 they earned in premiums, they lost $5 in responding to incidents.
Due to the rising costs associated with cyber incident response, many insurance companies are beefing up their coverage requirements and now expect MFA to be enabled for the following types of services:
- All admin access (both internal and remote) to directory services, network backup environments, network infrastructure, endpoints, and servers.
- All remote access to the network, including employees and third parties.
- All email systems which can be accessed through a cloud service (e.g., Office 365).
While this may seem like a reasonable request up-front, it may also be used as a reason to deny coverage in the event MFA implementation is not up-to-par.
Facing the Challenge: Review your cyber insurance policies. Determine if they require MFA and if your current MFA implementation would be satisfactory in the event of an incident.
Challenge #2. Financial institution guidance about MFA is not very descriptive.
Various financial institution regulatory agencies and industry leaders also now expect multifactor authentication to be implemented, as discussed in this article over What is Multifactor Authentication? For example:
- FFIEC Authentication Guidance (August 2021)
According to the guidance, MFA is encouraged for "high-risk users," which are defined as users who have "access to critical systems and data; privileged users, including security administrators; remote access to information systems; and key positions such as senior management" (page 5). For additional information, read the full guidance.
- FFIEC Cybersecurity Assessment Tool
The following maturity declarative statements from the tool's "Access and Data Management" component include reference to multifactor authentication.
- Remote access to critical systems by employees, contractors, and third parties uses encrypted connections and multifactor authentication.
- Multifactor authentication and/or layered controls have been implemented to secure all third-party access to the institution's network and/or systems and applications.
- Multifactor authentication (e.g., tokens, digital certificates) techniques are used for employee access to high-risk systems as identified in the risk assessment(s).
- For additional information, download the PDF or sign up for Tandem's free automated version of the tool.
- CSBS Ransomware Self-Assessment Tool (R-SAT)
R-SAT Question 10 asks users to confirm that MFA is used for various circumstances, including access to cloud-based services, cloud email services, VPN remote access, and administrative access. For additional information, check out our R-SAT blog.
- NIST Cybersecurity Framework v1.1
While not specific to financial institutions, the framework references MFA in subcategory PR.AC-7, which states "users, devices, and other assets are authenticated (e.g., single-factor, multi-factor) commensurate with the risk of the transaction." For additional information, download the framework.
While these guidance references are prescriptive, they are not overly descriptive as to how these recommendations are to be accomplished.
Facing the Challenge: Implementing a control, such as MFA, needs to be focused on protecting likely entry points, in addition to those which could cause significant potential damage, if compromised. Start considering how MFA could most effectively be implemented to mitigate the risks facing your organization.
Challenge #3. It is unfeasible to implement MFA everywhere.
Perhaps the greatest challenge with MFA, especially in consideration of increasing requirements, is that it is currently unfeasible to implement everywhere.
For example:
- It is not currently possible to enable MFA on Active Directory (AD) or SQL Servers. One can enable MFA on the systems which allow administrators to access these programs, but not the programs themselves, as they typically do not support integration with MFA applications.
- It is also not currently possible to enable MFA on service accounts. Service accounts often run with elevated privilege, but are not connected to any particular user, making it impossible to authenticate using MFA.
- To complicate matters further, there are multiple ways to authenticate as a Windows domain admin or to elevate privileges, once authenticated. Some examples could include running certain command lines, PowerShell scripts, windows management protocols, or User Account Control (UAC).
While applying MFA everywhere may sound like a dream come true, technological limitations currently prevent that dream from becoming a reality.
Facing the Challenge: Determine what you can secure with MFA and apply compensating controls for what you cannot. Based on your organization's long-term technology strategy, it may be beneficial to consider the possibility of moving certain systems to the cloud (e.g., Azure, AWS, etc.). That said, while many cloud solutions support MFA for access, they also present an entirely different set of risks and would not be a wholesale security solution in-and-of themselves.
Challenge #4. MFA is not infallible.
While MFA is an appealing control to consider, it is certainly not infallible and should not be implemented lightly. For example:
- It is important to recognize that anybody who has administrator access also has the ability to turn MFA off. If you are depending on MFA as a security control for administrators, there must be validation implemented to ensure it is not disabled.
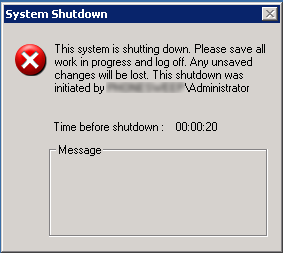
- MFA is a preventive control. Unfortunately, this can mean that when MFA methods are incorrectly configured or fail to work, it can result in administrators being locked out of their systems, which could cause significant damage to the organization.
- When controls, like MFA, cannot be implemented universally, it leaves the entire environment vulnerable by proxy. While applying MFA in certain areas or to certain users can limit exposure, the more security gaps you can close, the better.
Facing the Challenge: Implementation of MFA is not only a technical decision. It is an enterprise-wide strategy. Start the conversation by including relevant personnel in the decision-making process. Assess the impact of MFA on operations and make sure plans are in place to limit negative consequences.
Challenge #5. MFA can be expensive to implement.
While MFA is becoming more widely available, implementing it can still require a significant investment of time and money, as "one MFA to rule them all" does not exist. Every system has its own form of MFA. For example, some systems support:
- Proprietary MFA solutions, such as Duo MFA, Palo Alto GlobalProtect, RSA SecurID, Symantec VIP, etc.
- Solutions built on the Time-Based One-Time Password (TOTP) standard, such as Google Authenticator, Microsoft Authenticator, Twilio Authy, etc.
- Native MFA solutions, built into the application, such as how the Tandem Mobile App can be used as an MFA option for Tandem access.
Since systems use a variety of MFA options, it is up to each organization to ensure they select the right solution for them and ensure adequate coverage.
Facing the Challenge: If you do not currently have MFA implemented, begin planning for it now. If you need assistance, there are managed security service providers (MSSPs) with expertise in this area, such as CoNetrix Technology. If you would like assistance with selecting and implementing the right MFA solution, contact us.
Conclusion
MFA is a highly effective control when it comes to reducing the risk of various threats, but it comes with its own set of challenges and risks. As you consider your current and future MFA plans, take a step back and answer the question: Are you trying to check a box or are you trying to mitigate a risk?
A layered security program is always going to be the most effective way to face the cyber challenges of our time. While MFA is a helpful component of this program and should be used when feasible, it is not the only control you need. You have to use many controls to create a layered security program. For additional information about how you can secure your systems or to learn more about IT managed services, visit CoNetrix.com/Technology.