CoNetrix recently assisted two customers with targeted phishing attacks in which the attackers attempted to redirect wire transfers. This activity is not new, however, some of the tactics utilized in the attack are noteworthy and provide insight into how organizations can better protect themselves.
How did the attackers gain entry into corporate accounts?
The entry point for the attackers was corporate email accounts that were exposed to the Internet and accessed using a web browser. The email accounts of the victims were compromised by guessing passwords or reusing previously-compromised passwords. Once access was gained to the email accounts, mailbox rules were configured to direct emails about wire transfers to the "RSS Feeds" folder. This effectively hid the email messages from the victim, while allowing the attacker access to them.
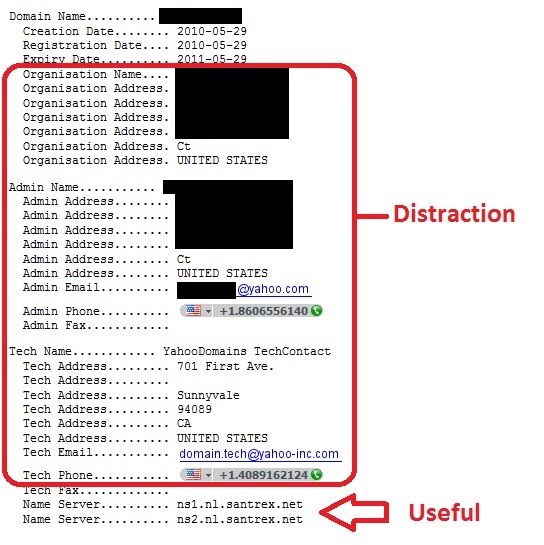
Next, the attacker sent email messages from a domain name similar to the domain name of the compromised email account. The fake messages said the previous email messages concerning money transfers were in error and provided different destination bank routing and account numbers where the money would be accessible by the attackers.
Take steps to mitigate the risks of phishing attacks
In these cases, the fraudulent email messages were noticed by the recipients and the attacks failed. However, these attacks are routinely successful, and it is necessary to take steps to mitigate the risk, especially when corporate email accounts are accessible using a web browser (e.g. Office 365, Outlook Web Access (OWA), cloud-hosted email, any email account that can be logged into using a web browser and public Internet access).
- Review your organization's email services to see if Internet-facing email access is enabled. One way to do this is to ask the question, "can we log in to our email accounts using a web browser from any Internet connection (e.g. a coffee shop, at home, at a hotel)?"
- If Internet-facing email access is enabled disable access for employees who do not need it.
- For employees who need Internet-facing email access, enable dual-factor authentication.
- Look for inbox forwarding or redirect rule changes. Logging for these changes can be enabled in the email system's administrative console.
- On firewall or intrusion prevention devices, enable rules to block traffic that is sourced from countries where known malicious traffic originates.
- Utilize security event monitoring technologies to monitor web server logs for abnormal login activity.
- Do not rely solely on email or other electronic communications for initiating or modifying financial transactions. Implement out-of-band approval procedures such that financial transactions and changes to financial processes must be verified using a different form of communication. For example, if a request to change a receiving bank account number is initiated via email, it must be verified via a phone call to a number that is already on file.