In most of our Exchange environments, we'll have port 443 open to the outside for ActiveSync and Outlook Anywhere. When you do that, you'll also open up OWA and ECP to the outside. If you'd like to keep access for ActiveSync and Outlook Anywhere open but would like to block OWA and ECP you can follow the steps below.
There are a few ways to block OWA and ECP to external addresses, but the best method is probably to use the IP and Domain Restrictions feature in IIS. This feature isn't available by default, so you'll have to install it.
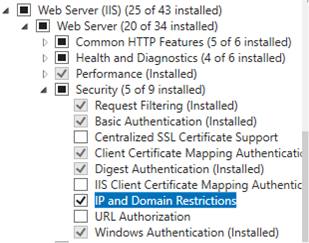
To install it, open Server Manager, select Add Roles and Features. In the Add Roles and Features Wizard, under Server Roles, expand Web Server (IIS), then expand Web Server, and then expand Security. Then click the checkbox for IP and Domain Restrictions.
Once that installs, open IIS, expand Default Web Site and click on the OWA Virtual Directory. You'll now see the IP Address and Domain Restrictions feature available.

When you open that feature you can add an Allow Restriction Rule or a Deny Restriction Rule. My suggestion would be to add the subnets you would like to be able to access OWA and ECP (internally and externally) and then change the default behavior for unspecified clients to Deny.
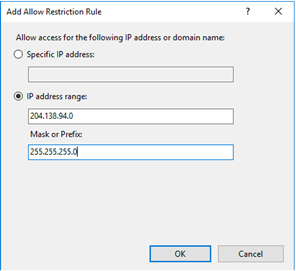
To add an entire subnet as an allowed subnet, click Add Allow Entry, and then in the Rule settings enter the IP info. You can add an individual IP, a range, or a subnet.
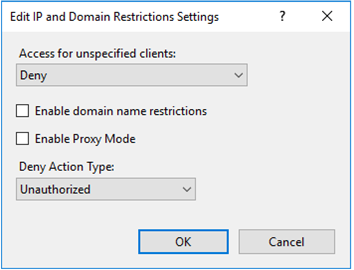
To change the default behavior for unspecified clients, click Edit Feature Settings and set Access for unspecified clients to Deny.
Repeat the same steps on the ECP virtual directory. Once that has been completed restart the IIS service (iisreset) to apply the changes.
