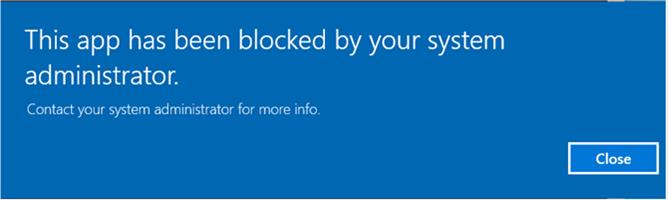
I was configuring a new Windows 10 PC for a customer and logged in under the local administrator account. I tried to open Edge but received a notification that Edge could not be opened by the built-in administrator account.
After some research, I discovered that Microsoft has become distrusting enough of the local administrator account that they prevent it from opening Microsoft Apps. This was actually introduced with Windows 8, but Windows 10 introduced Edge, which is potentially the first widespread use of Microsoft App.
The options to fix this are to either disable UAC, or adjust group policy to allow the local admin account to access Apps. The details of the issue and the options for a fix are included in this link: https://4sysops.com/archives/why-the-built-in-administrator-account-cant-open-edge-and-a-lesson-in-uac/