Quite frequently on information security audits we find machines where group policies have been applied incorrectly or not at all. The IT administrator swears the policy is working, but the policies haven’t always taken on machines. What we can do in that situation for Windows XP machines is use GPupdate.exe, Rsop.msc, and GPresult.exe to find out more information. [more]
GPupdate
After you make changes to group policies, you may want the changes to be applied immediately, without waiting for the default update interval (90 minutes on domain members and 5 minutes on domain controllers) or without restarting the computer. To make this update, at a command prompt, run the Gpupdate.exe utility.
RSoP
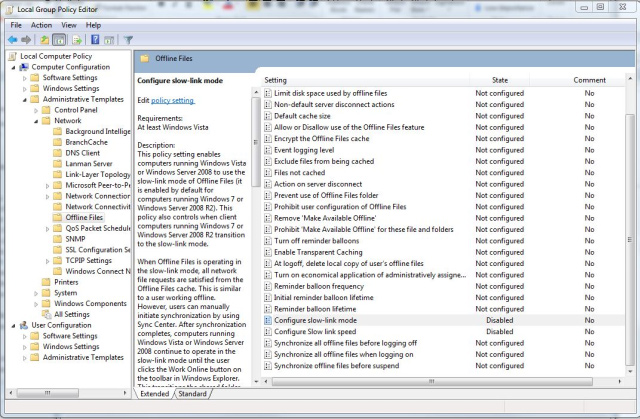
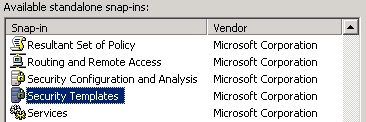
The Resultant Set of Policy MMC snap-in has a nice interface and is easily used. Just go to Start, Run and enter rsop.msc. This will flash up a quick screen with a summary of the environment it’s processing.
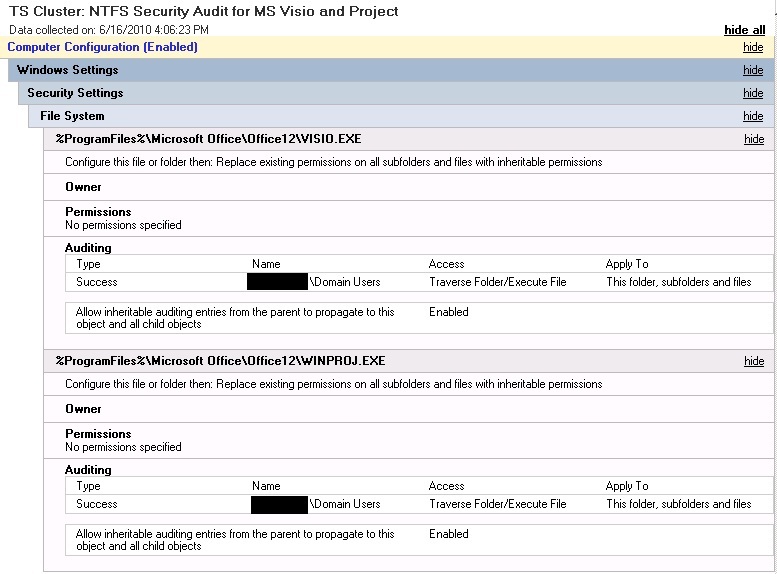
When the progress reaches 100%, it will pull up a report for the policies upon which the computer and the user are having applied. You can browse the list, which mirrors the Group Policy Management Console, and see which policies the machine is seeing, which might not quite match what you’ve set in the Active Directory server.
You can also use this to diagnose any errors. For example, if a software deployment isn’t coming through for some reason, you can verify that it has access to the policy and has received the command. You can also see any related errors to help your troubleshooting.
GPResult
Starting with Vista SP1, RSoP no longer shows all of the group policies that a computer might have being applied to it. Instead, Microsoft recommends that you use the command line tool GPResult. Just open the Command Prompt and type: gpresult
Being a command line tool, it opens up the possibilities to include it in scripting. There are a large number of options you can use with GPResult to get exactly what you want. You can use it to create a nicely formatted HTML or XML report and you can also use it to run remotely on another system and as a different user (provided you know the password).