Example Error Message
Delivery has failed to these recipients or groups:
A prolem occurred while delivering this message to this email address. Try sending this message again. If the problem continues, please contact your help desk.
The following organization rejected your message: xxxxxx.ess.barracudanetworks.com.
Overview
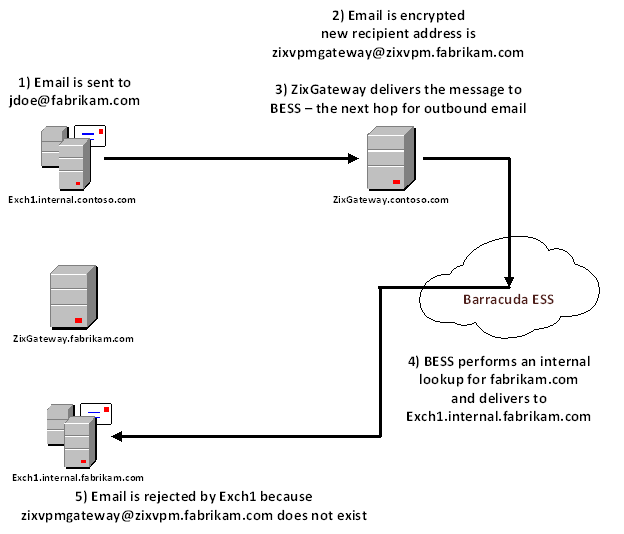
This post is intended to provide a high-level overview of the routing and delivery between two companies who utilize a ZixGateway and the Barracuda Email Security Service to encrypt and scan their messages. In addition, this document will cover a common delivery issue between these same companies. [more]
Prerequisites
- Both companies have a ZixGateway Email Encryption virtual or physical appliance
- Both companies use Barracuda Email Security Service for antispam/antimalware scanning
- The sending company has configured the Barracuda Email Security Service to scan all outbound email
Procedure
When a ZixGateway customer sends an email to another ZixGateway customer, the sending appliance is aware that both customers use Zix encryption and will automatically encrypt the email before delivering it. This is seamless to end users on both sides and makes email delivery between the two automatically secure.
At this point, any mail gateway will look up MX records for zixvpm.recipientdomain.com and deliver it normally until the message reaches the destination ZixGateway. This recipient gateway will unwrap the encrypted attachment (i.e. decrypt the email), and deliver it as normal to the original recipient.

;; ANSWER SELECTION:fabrikam.com. 3600 IN MX 10 d12345a.ess.barracudanetworks.com.fabrikam.com. 3600 IN MX 20 d12345b.ess.barracudanetworks.com.;; ANSWER SELECTION:zixvpm.fabrikam.com. 3600 IN MX 20 Zixgateway.fabrikam.com.