 "The Cloud" is a recently coined and hot term that makes the technology seem like it's been recently developed. However, service offerings that would meet today's definition of cloud-based computing have been around since the 1950s, according to Wikipedia. Amazon.com was one of the first companies to offer elastic computing, a precursor term for "The Cloud", so they are sometimes credited with developing the concept of cloud computing. In reality, it is unclear who came up with the term "The Cloud."
"The Cloud" is a recently coined and hot term that makes the technology seem like it's been recently developed. However, service offerings that would meet today's definition of cloud-based computing have been around since the 1950s, according to Wikipedia. Amazon.com was one of the first companies to offer elastic computing, a precursor term for "The Cloud", so they are sometimes credited with developing the concept of cloud computing. In reality, it is unclear who came up with the term "The Cloud."
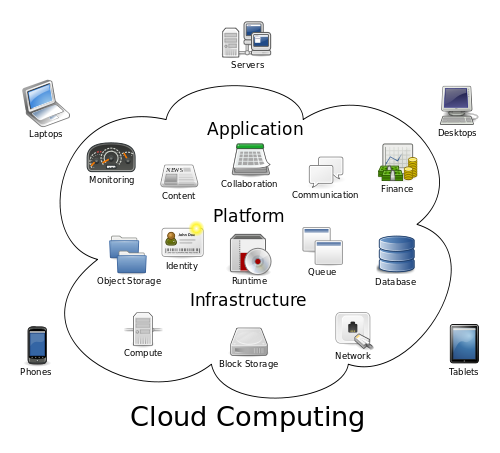
For those that are curious, the National Institute of Standards and Technology (NIST) offers the following formal definition of cloud computing:
Cloud computing is a model for enabling ubiquitous, convenient, on-demand network access to a shared pool of configurable computing resources (e.g., networks, servers, storage, applications, and services) that can be rapidly provisioned and released with minimal management effort or service provider interaction.
Now that's a government definition, a 42 word sentence. The definition alone gives us an indication of "The Cloud's" complexity and reach. Simply put, "The Cloud" is any IT product or service provided by a third party over a network connection. That may be too simple for some, but it boils it down nicely. If your financial institution utilizes hosted email, online data storage, or an outsourced core banking application, you are technically in "The Cloud."
A common problem with the adoption of cloud services is how to conduct appropriate due diligence before using cloud technologies. Standard vendor management practices can be applied to cloud services; however, due diligence needs to be increased and focused to cover the special compliance and security control problems introduced by "The Cloud." It is common to see a general lack of focused due diligence when financial institutions review cloud services, mostly because organizations just don't know the correct topics to cover and how to document the review. For example, if you're currently using "The Cloud" and cannot answer the following basic questions about the service, you probably need to re-evaluate your cloud diligence processes:
- Where are the servers physically located that store the financial institution's data?
- How is my data protected while in transit and while in storage?
- Has a recent third party audit been conducted on the cloud provider?
Although these questions are just the tip of the iceberg, I mention them to illustrate the importance and necessity of effective cloud due diligence.
Two additional problems I commonly come across when conducting network evaluations are the lack of clear policy regarding cloud usage and the general ease of cloud implementation. Financial institutions are well aware of the requirement for IT policy, but the task to keep policy current with advancing technology is an ongoing problem. With regard to "The Cloud", financial institutions should adopt cloud usage guidance and apply relevant pieces to their Acceptable Use Policies.
Although "The Cloud" can be used for very complex IT requirements, it's sometimes the simplest cloud usage that causes security or compliance issues. It could be something as simple as an employee forwarding company email to a personal email box hosted in "The Cloud" (e.g., Yahoo! Mail, Hotmail, Gmail). While this is an email policy problem, it could also be considered a cloud policy issue. A situation like this could present a serious problem if the cloud e-mail provider happened to get compromised, especially if customer data was involved. Formal incident response and notification would then be required.
Another problem, specifically with cloud storage services, is the general ease of access and implementation of cloud storage. It is not unusual for companies or individual employees to start using readily available cloud storage services, such as DropBox or iCloud, for personal or business tasks without proper evaluation or authorization. Some of these services require a freely available executable file and others do not; they simply require Internet access. This situation could present a serious problem if confidential bank or customer data is being stored. Some of these services offer data encryption capability, but the question is: who holds the key to decrypt the information stored in the cloud? If the answer is anyone other than the financial institution itself, then there could be a problem. What if the cloud storage provider is compromised, including the encryption keys? Then, cyber criminals could have access to all the data, including sensitive customer information. In scenarios where the bank is unaware that online storage is in use, proper due diligence in evaluating relevant controls was surely skipped. Also, in this scenario, it is unlikely the bank has a contract or separate confidentiality agreement with the cloud storage provider, a requirement if storing customer online.
"The Cloud" offers advanced IT solutions, but definitely not without risk. Proper due diligence and risk management should be in place to effectively deal with "The Cloud." To help promote cloud best practices, a not-for-profit organization called the Cloud Security Alliance has created several documents to help organizations ensure they go through the proper evaluation processes and have a framework to facilitate such diligence. These documents are freely available at: https://cloudsecurityalliance.org/.

